(1) $25 Amazon Gift card & (10) e-book copies of the “shorts” in the Enigma Serie

4 Wills Tour Day 3
Breakfield and Burkey wanted to share the research requirements of the Enigma Series.
Our day jobs require we stay abreast of current technology trends. This gives us the ideas or focus for a given book. We perform additional research for specific details we weave into a story, to verify the capabilities. Then we weave the storyline around real technology that is available, while allowing the right characters to use that knowledge. In our stories the Heroes and Villains are technologically savvy, so it often becomes like a chess game of who finds the next play or block first.
For example, in the latest story, The Enigma Threat, we spent a good deal of time research abandoned satellites still orbiting the earth. The general assumption is that once the satellites duty cycle was completed, it would simply route into the atmosphere where it would burn up during reentry. As it turns out, there are numerous satellites still orbiting the earth, but not used or in some cases actively responding to communications. We had a field day with this revelation in the story, which you won’t want to miss.
We want to share a few of the juicy tidbits into The Enigma Threat. Research for us comes from collaboration with many people, insights of plans for upcoming offerings, and volumes of white papers. However, we also take comments from beta readers and reviewers to improve our stories. One of our beta readers offered some insight we refused to ignore. They stated, “I hate reading author’s stories that use the same formula for each book in the series. I want fresh and different, but something that makes me think.”
Toward that end, we’ve had reviewers who have done several of the books in the series. One such reviewer stated, “These authors don’t fall into a familiar pattern for a story plot. If you think this will be the same as last time, you will be disappointed.” We like to have some twists to make people think about the possibilities. We like quoting Arthur C. Clarke’s Don’t give me more, give me better. Breakfield and Burkey heartily subscribe to this mantra.
Our research is always turning up something new. Once upon a time business determined the direction of technology. That shifted, as Burkey often suggests, when the demands of users in our digital world shifted to optimizing experience of the individual first. All the devices we have at our fingertips highlight that with a myriad of applications, some safe, some questionable.
This helps provide for a fresh new attack vector always ahead of the good guys. In cyber security the hackers and crackers are always ahead of the good guys. Many times, hackers take this route of breaking something as part of a challenge, or to say they could. Sometimes they look for the profits. Today the profitability is unbelievably high. Each new Darknet threat comes as an unexpected guest who will not leave until counter measures are built. In our world, the fiction is real. We like our characters to bring readers into our Enigma Universe.
Sadly, people often don’t believe they are vulnerable until an event. Most people say, “I usually don’t think about security but when I do it’s always too late”. The events can be modest or overwhelming such as a data center gutted by cyber malware, their daughter calls crying that she needs $4,000 in cash or she is going to jail, or all the medical records of a hospital will be published on-line unless $250,000 in Bitcoin is transferred in the next 24 hours. Cyber extortion is alive and unfortunately well in today’s age of instant communications. With it comes instant infections. These viral infections are not just of computer operations but also the poisoning of people’s thinking with false information.
This is the research we do daily to build technically accurate problems that our heroes of the R-Group must remedy. The frightening reality is the Darknet attack vectors are aimed at the individuals as much as companies. Our characters and our scenarios are built on people who have crossed our paths in truly vulnerable situations.
We hope the readers of your blog, take a few minutes to review our Kickstarter campaign. There are additional details on The Enigma Threat, the book trailer, and special backer only offers.
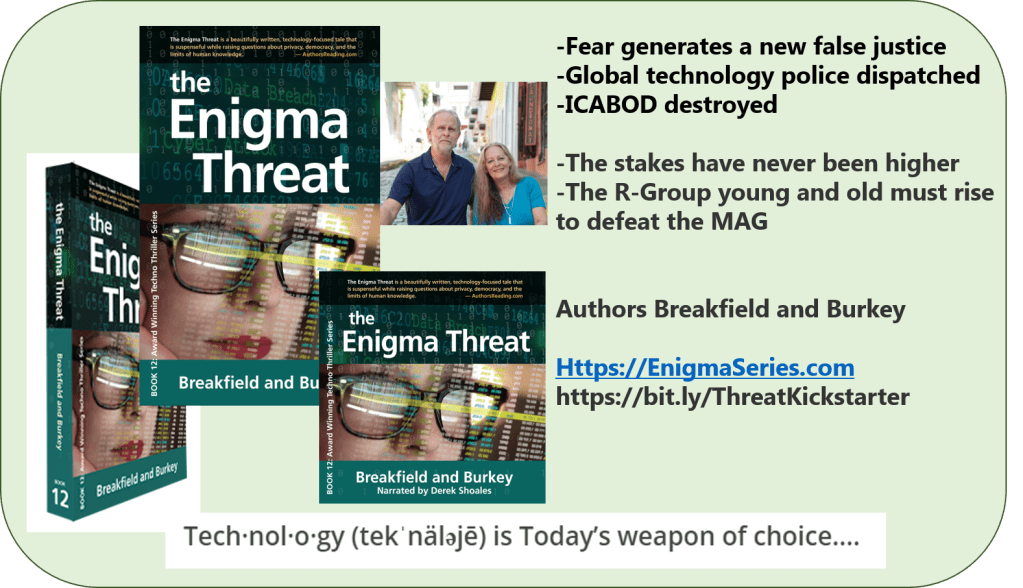
BREAKFIELD AND BURKEY TOUR SHEET – THE ENIGMA THREAT
Video teaser – https://youtu.be/JQSQdAjCLPE
BLURB:
In the new digital world, there is no tolerance for privately owned supercomputers. Globally, computers are hunted and destroyed for the greater good, by the new cyber police CESPOOL. The information this group receives is manipulated by subversive hidden machine learning devices, the MAG running on the dark net.
Judith and Xiamara are freebooters who steal machine time for their PaaS, porn as a service business. The machine they chose for delivery is the last untapped supercomputer not in the hands of a sovereign. Their activity is spotted by the MAG, but the renegade R-Group steps in to alter the outcome. Leroy teams up with Zara to help these opportunists escape prosecution. They are drafted as reluctant participants in the fight.
Jacob and Quip are trapped in the Chihuahuan Desert trying to reconstruct the base of ICABOD’s logic core. The stress of their isolation is taking a toll. Their wives and children are safe in Brazil for the time being, but Interpol is prowling for answers.
The R-Group has assembled a way to communicate with orphaned satellites. While the next R-Group plans the ultimate honey pot to trap their nemesis who is driving their corrupted agenda. The odds are against R-Group’s success, but they have creative surprises on their side.
The stakes have never been higher. The R-Group young and old must rise to defeat the MAG.


BIO:
Breakfield is a 25+ year technology expert in security, networking, voice, and anything digital. He enjoys writing, studying World War II history, travel, and cultural exchanges. He’s also a fan of wine tastings, winemaking, Harley riding, cooking extravaganzas, and woodworking.
Burkey is a 25+ year applied technology professional who excels at optimizing technology and business investments. She works with customers all over the world focusing on optimized customer experiences. She writes white papers and documentation, but found she has a marked preference for writing fiction.
Together they create award-winning stories that resonate with males and females, as well as young and experienced adults. They bring a fresh new view to technology possibilities today.
Email: Authors@EnigmaSeries.com
Website: www.EnigmaBookSeries.com
Blog: https://EnigmaBookSeries.com/the-enigma-chronicles/category/blog-statement/
Connect and follow on Social Media:
LinkedIn: https://www.linkedin.com/in/charlesbreakfield and
https://www.linkedin.com/in/roxanneburkey
Twitter: https://twitter.com/EnigmaSeries
and https://twitter.com/1RBurkey
Facebook: https://www.facebook.com/TheEnigmaSeries/
YouTube: https://www.youtube.com/channel/UC6Vz4x5ctTnx3yUhZk1OJkw
Pinterest: https://www.pinterest.com/enigmseries/
Instagram: https://www.instagram.com/enigmabookseries/
Bublish: https://bublish.com/author/breakfieldandburkey
RRBC: https://ravereviewsbookclub.wordpress.com/about-breakfield-burkey-enigmaseries-rrbc-rrbc_community/
To follow along with the rest of the tour, please visit the authors’ tour page on the 4WillsPublishing site. If you’d like to book your own blog tour and have your book promoted in similar grand fashion, please click HERE. Thanks for supporting these authors and their work!



It’s so scary to read about the security threats that are everywhere these days. I enjoyed this post and apologize for being late to the party. I wish Breakfield and Burkey the best and thank you for hosting, Joy!
LikeLike
I found your info about the abandoned satellites fascinating – I wonder how much ‘space junk’ is still out there?
LikeLike
Great question! You may have launched a new career for someone or given Elon Musk an idea for a new company. I can see it now “Satellite Sanitation Squad! Got space junk? Call us!”
LikeLike
Thanks, Joy, for continuing this great tour. Rox and Charles, you’re so right: No one things anything will happen to their computer security until it does. And then what? Ask Microsoft. Ask Starfire. Ask our local health insurers. Ask the hospitals, that are being held for ransom before they can regain access to their patient records. I’m so glad that you are writing about this. Sometimes fiction can bring these things alive and people will believe it’s real.
LikeLike
Wanda, ironically we have people grousing at us for writing fiction that keeps coming true. Now if we could only write about fictitious lotto numbers that come true…
LikeLike
I can imagine that a lot of research is required to write in this genre, even if you are in the industry. It all sounds fascinating. Thanks for hosting, Joy.
LikeLike
Robbie, thanks for stopping by! It’s funny but we never really think about doing “research” because we work in the high tech industry. We don’t see how it can be research if it is so much fun.
Breakfield
LikeLike
Rox and Charles Congratulations!
LikeLiked by 2 people
Thank you, Shirley. Happy New Year to you and yours. Thanks for following us. Didn’t Joy do some awesome hosting?
LikeLike
Yes Rox. Joy is doing some awesome hosting. She always does.
Happy New Year All!
LikeLike
Shirley, thanks for the well wishes madam.
Breakfield
LikeLiked by 1 person
I don’t know if I’d ever be able to do as much research as the two of you do. Wow. Your kickstarter looks great. Good luck, Rox and Charles. Thanks for hosting, Joy. 🙂
LikeLiked by 1 person
Thank you so much Yvette. Appreciate the feedback and your support. Joy you help make us shine.
LikeLiked by 1 person
Hi Rox, Hi Charles, Hi Joy,
Rox and Charles, your story is engaging. I am a Star Trek fan and especially loved the Series with the Voyager. I have every Disc of that Series.. I am also impressed with your research. I too don‘t like to read a book with the same old pattern every time the author writes. Therefore, I applaud your stepping out there and challenging the reader to follow and think.
I do wish you both much success with The Enigma Threat. In fact with the whole series.
Thank you for sharing about your level of research.
Joy, I thank you for opening your blog to host Rox and Charles.
All the best to all of you and have a safe crossover into 2021.
Shalom aleichem
Pat
LikeLiked by 1 person
Hi Pat, so very kind of you to say, thank you. Joy is a peach for hosting this and we love all the visitors sharing our fun. Happy New Year. Rox
LikeLiked by 1 person
Thank you for hosting, Joy. For Charles and Rox, I hope you are well on your way to selling a million. Good luck on the rest of your tour.
LikeLiked by 1 person
OMGoodness, We are all about making a million readers delighted! Thank you for visiting Joy’s awesome blog, John. Happy new year.
LikeLike
A fabulous tour thus far! Thanks for hosting Rox and Charles, Joy!
LikeLiked by 1 person
It is in a word, fantastic!
LikeLike
Hi Joy, What a lovely blog to be front and center on. We appreciate your support and that of your followers. May the new year bring you peace, joy, and more hope than any prior year. Rox!
LikeLike
You are very welcome, Rox. I wish you a very successful tour and a prosperous year!
LikeLike
Hi, guys, I am thrilled to have you on my blog today! I hope you are having a wonderful tour so far! Good luck!
LikeLiked by 1 person